LOCK YER DEVICES! –
The Muhstik botnet has targeted other IoT devices. Now it’s attacking Tomato routers.
Dan Goodin – Jan 23, 1579638423 8: (UTC UTC)
The Muhstik botnet came to light about two years ago when it started unleashed a string of exploits that attacked Linux servers and Internet- of-things devices. It opportunistically exploited a host of vulnerabilities, including the so-called critical Drupalgeddon2 vulnerability disclosed in early in the Drupal content management system. Muhstik has also been caught using vulnerabilities in routers that use Gigabit Passive Optical Network (GPON) or DD-WRT software. The botnet has also exploited previously patched vulnerabilities in other server applications, including the Webdav, WebLogic, Webuzo, and WordPress. Tuesday researchers from Palo Alto Networks said they recently detected Muhstik targeting Internet routers running Tomato , an open-source package that serves as an alternative to firmware that ships by default with routers running Broadcom chips. The ability to work with virtual private networks and provide advanced quality of service control make Tomato popular with end users and in some cases router sellers.
The exploit causes Tomato routers that haven’t been locked down with a strong password to join an IRC server that’s used to control the botnet . The infection also causes the routers to scan the Internet for servers or devices running WordPress, Webuzo , or WebLogic packages that are vulnerable. The image below shows the execution flow of the new variant as it combines various modules that scan the Internet for vulnerable servers:
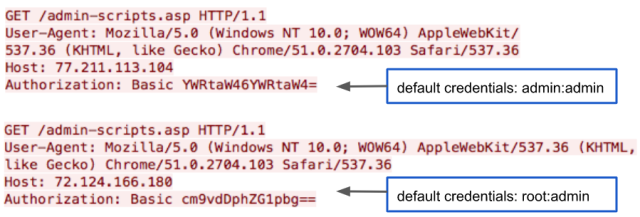
“The new Muhstik botnet variant demonstrates that IoT botnet keeps expanding the botnet size by adding new scanners and exploits to harvest new IoT devices, ”Palo Alto Networks researchers Cong Zheng, Asher Davila, and Yang Ji wrote in a post titled Muhstik Botnet Attacks Tomato Routers to Harvest New IoT Devices . “Botnet developers are increasingly compromising IoT devices installed with the open source firmware, which often lack the security updates and maintenance patches necessary to keep devices safeguarded. End users should be cautious when installing open source firmware and must follow the security guidelines in the firmware manual. ”
People looking for signs that their router has been infected should check logs for access to the following IP addresses or domains:
360 [.]  . 452 [.] . [.] 42 , hxxp: //y.fd6fq (s6df) (q) (sdxfg) (eu / nvr)
. 452 [.] . [.] 42 , hxxp: //y.fd6fq (s6df) (q) (sdxfg) (eu / nvr)
hxxp: //
Tuesday’s blog post also provides the names and hash digests for seven files used in the router compromises. Although Muhstik has been known to exploit firmware vulnerabilities in GPON and DD-WRT, there’s no indication the new variants are using any flaws in Tomato. That suggests that weak passwords are the sole means the botnet has for taking control of routers. People should make sure they have updated the default credentials with a strong password. 1579638423 Read More





GIPHY App Key not set. Please check settings